Aria stories - Page 100
Aria is where cutting‑edge technology, security, and AI‑driven innovation intersect. The stories tagged here span everything from next‑gen cloud and data platforms to ransomware trends, smart infrastructure, and the fast‑evolving world of generative and agentic AI. If you want to understand how tools like AI copilots, LLMs, and real‑time analytics are reshaping everything from finance to healthcare to manufacturing, this is your starting point.
Dive into in‑depth coverage of cybersecurity – botnets, ransomware variants, mobile malware, zero‑day exploits, and the shift to continuous, intelligence‑led defence. Explore how data centres, networks, and observability platforms are being redesigned for AI workloads, sustainability, and hybrid cloud. Follow the rise of AI in everyday products too, from wearables and smart home devices to vehicles, retail experiences, and next‑gen collaboration tools.
Aria isn’t just about the technology itself, but about its impact: on regulation, trust, jobs, skills, and digital resilience. Here you’ll find expert commentary, major vendor announcements, case studies, and long‑form explainers that help you connect the dots between infrastructure, security, AI, and real business outcomes. If you’re responsible for strategy, architecture, risk, or innovation, the Aria tag will keep you ahead of what’s coming next.
New travel app to enable direct marketing to tourists

Hands-on Review: Belkin QODE Ultimate Pro iPad Keyboard

How MyRepublic proved Gbps speeds aren't required
Hands-on Review: ViewSonic DLP Projector PJD5555W

Sierra Wireless launches new, rugged, LTE gateway

Four proven ways to speed up your broadband

Hands-on Review: Huawei P8 Lite

Casio EcoLite projector wins Award of Excellence
So blocking good: ScaleIO now available as software, nodes or rack-scale

Adobe MAX: Software heavyweight responds to digital change

Are your systems already compromised? Probably.

3CX releases latest update to phone system
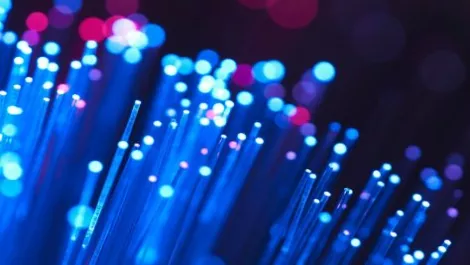
Local Government NZ welcomes UFB tender

Are you ready for the third wave of the digital age?

Don't let cybercriminals hold your business hostage
Cost of data breach skyrockets: What can you do?

Windows 10 upgrade causing UFB congestion

Time-to-detection key to prevent sophisticated cyberattacks

Preparing your IT environment for mobility
